Raspberry Pi: OpenVPN vs WireGuard, which one is the best?
If you are looking for a VPN software, OpenVPN is still the most popular solution, but WireGuard is a suggestion that we hear more and more in the last years.
Where are we exactly? What are the differences between OpenVPN and WireGuard?
That’s what I will try to answer in this article.
OpenVPN and WireGuard are two open-source solutions to create virtual private network (VPN).
OpenVPN is the standard, created in 2001, and running most VPN in the world.
WireGuard is a recent solution (2016), promoting better performances that should not be overlooked when creating a new VPN.
In this post, I will start by an overview of each solution, and then compare them point per point.
If you’re looking to quickly progress on Raspberry Pi, you can check out my e-book here. It’s a 30-day challenge where you learn one new thing every day until you become a Raspberry Pi expert. The first third of the book teaches you the basics, but the following chapters include projects you can try on your own.
OpenVPN

History
So, as I told you in introduction, OpenVPN is the old solution, created in 2001, about 20 years ago!
Do you remember 2001? Google was a young company, Apple had just released the iPod, Microsoft released Windows XP, etc. It was another age 🙂
OpenVPN was created in this period, with most of the population without Internet access at home, so it was really a revolution for bigger networks (even if IPsec was already there).
OpenVPN quickly grows to be adopted by most brands and companies, and is now the standard to create VPN.
Encryption methods
I don’t want to be too technical in this post, so I’ll not give too many details about the security part, but just as a reminder, the goal of a VPN is to protect your data by encrypting them on the network between your computer and the server.
To do this, there are several protocols available, and OpenVPN mainly use OpenSSL. OpenSSL provides SSL and TLS protocols
It’s the same technology as for HTTPS website, so it’s a standard in cryptographic protocols.
Join Our Community!
Connect, learn, and grow with other Raspberry Pi enthusiasts. Support RaspberryTips and enjoy an ad-free reading experience. Get exclusive monthly video tutorials and many other benefits.
Learn moreThe goal with these tool is to access a home network (a company network in general) from outside. Don’t confuse this with accessing Internet via a secured tunnel, which is done by providers like NordVPN (that you can also install on Raspberry Pi, as explained there).
Authentication
When using OpenVPN, you need to authenticate on the VPN server to connect.
This can be done with three methods :
If you are lost in all these new words and abbreviations, request my free Raspberry Pi glossary here (PDF format)!
Download now
- Pre-share keys : The server will generate keys to use when you connect, to prove who you are.
- A certificate-based method : More secure but it’s the same principle (same thing as for HTTPS websites).
- Username / password : Not mandatory, but you can add this level of security with one of the others.
I generally use certificates + username/password, but you can configure it as you want depending on your current needs.
Platforms
With 20 years of operation, OpenVPN has had time to be included in most solutions and all operating systems.
You will almost always find a way to create an OpenVPN server on any router of the market.
For example, I use Pfsense a lot at work, and we build VPNs with the OpenVPN module integrated in Pfsense.
Watchguard was another firewall I used before that, and it also included an OpenVPN server (it’s a red box like this).
So, it should not be complicated to create a server. And obviously, you can install it manually on any operating system.
For clients, OpenVPN is available on most platforms:
- Windows
- macOS
- Linux / BSD
- Android
- IOS
You can download the applications directly on the OpenVPN website.
You can even create an OpenVPN Access Server on AWS (the cloud solution from Amazon).
OpenVPN and Raspberry Pi
The goal here is not to explain how to install OpenVPN, but for information, you can install it easily on Raspberry Pi.
It’s available in the Raspberry Pi OS repository, or you can download the source code here.
The installation is a bit more complicated, so if you try to do this on your Raspberry Pi, I recommend checking this tutorial I made on how to install OpenVPN on Raspberry Pi.
Another solution, if you want to go faster, is to try PiVPN to do almost everything for you. Run the command, answer the questions, and customize it after the installation if needed.
WireGuard

Let’s see what the challenger has to offer now 🙂
History
WireGuard is a very new solution for VPN on the market.
Created in 2016 and developed during at least 2 years in a beta version, it’s very young.
But in January 2020, Linus Torvalds accepted to include WireGuard in the Linux Kernel, and it was a big promotion for this software.
We can now consider it seriously for new projects.
The main goal of the author is simply to replace any other VPN solution by WireGuard (yes, just that ^^).
As you can see on the logo, they promote their project as faster, safer and lighter.
For the lightweight, there is no doubt. The WireGuard source code is made with 4000 lines, while OpenVPN has 150 times more lines than that.
That doesn’t mean it’s safer or faster, but in any case it’s clearly lighter.
We’ll see now what really change for the user and the administrator.
Encryption methods
As WireGuard is a younger project, it includes some of the most recent technologies.
For symmetric encryption, WireGuard uses Chacha2020 (also used by Google on Android). Curve25519 as a backup protection, BLAKE2s, SipHash24 and HKDF are also used for specific parts if you want to know, but for now just remember that WireGuard is using safe and fast protocols.
Authentication
For authentication, WireGuard is elementary.
It uses only public and private keys, as you would do with SSH authentication.
The server has its own secret key and know the list of users. On the client, you also have a secret key and the public key of the server that you will use to connect.
If you are lost in all these new words and abbreviations, request my free Raspberry Pi glossary here (PDF format)!
Download now
To add a new client, you just add a new peer on the server and it’s ready to use.
Once they exchanged their public key, the connection can be made.
Note: If you want to try WireGuard or OpenVPN, I have a video lesson available for the community members where I show you all the steps. You can join here and watch it directly if you are interested (with 10+ other lessons for Raspberry Pi and many other benefits).
Platforms
As you can see on the official website, WireGuard clients are available on most operating systems.
On Linux, it’s often available in the default repository of your distribution. For Windows and macOS there is an installer to download.
And on smartphone you can find an app in the store.
Clients are also directly included in some other solutions if you don’t want to do the installation yourself.
For example, if you are using NordVPN for other things, you can add a connection to a WireGuard server in it, through the Nordlynx technology. By the way, I have an entire article here on why and how to install NordVPN on Raspberry Pi.
To find a server in the solutions on the market is more difficult. The WireGuard project is probably too young to have had the time to be included in the most popular solutions.
But you can find a package on Pfsense, for example, and obviously install it manually on your system.
OpenVPN and Raspberry Pi
On Raspberry Pi, WireGuard is available in the default Raspberry Pi OS repository.
But the easiest way to install it is to use PiVPN.io
This script includes WireGuard since 2019 as an alternative to OpenVPN (you have the choice at the beginning of the installation).
I have a full article about WireGuard on Raspberry Pi here, check it out if you want to learn more and try it.
It's a free PDF guide containing every Raspberry Pi Linux command you should know!
Download now
Differences between OpenVPN and WireGuard
Support
As I already wrote previously, OpenVPN is available on almost any platform and many manufacturers are including the technology in their solutions (routers, firewall, etc.). Cloud hosting is also easy to find (with Amazon or other).
WireGuard is still too young to be largely integrated on network hardware, even if some manufacturers start to speak about it. But you can easily create your server on any Linux distribution, and on some other solutions like Pfsense.
Your choice will probably depend on the network you already have, and if you are ok to add or change some equipment or want to keep the same.
For users, there is no difference, both solutions are easy to install on Windows / macOS / Linux.
Performances
I didn’t do the benchmark myself for the moment, but I have seen everywhere that WireGuard, is not only promoting its speed, but is also much faster than other solutions.
It’s not astounding as it’s one of the main goal of the developers, and that the code is really limited to the minimum.
On the official website, you can find a benchmark they made with speed (megabits per second) and ping response (milliseconds).
It’s on their website, so I don’t know how we can consider that, but it seems that people are getting similar results in real life.
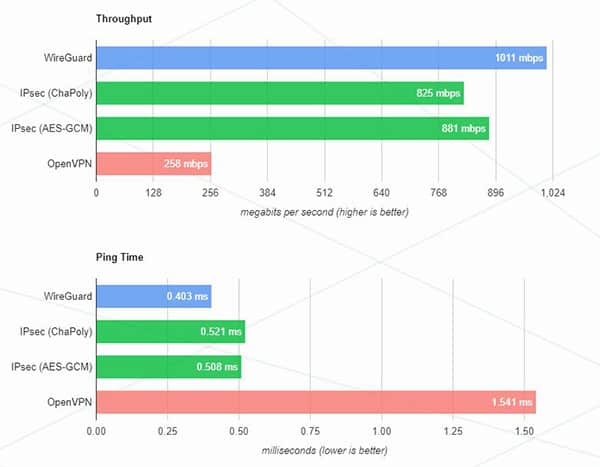
So, for performances, WireGuard seems to be way better than OpenVPN.
Interest
Also, another interesting thing I found thanks to Google Trends, is the interest in web search in the past 5 years for the two solutions.
OpenVPN seems to be gradually declining in the last few years, while WireGuard has an opposite trend.
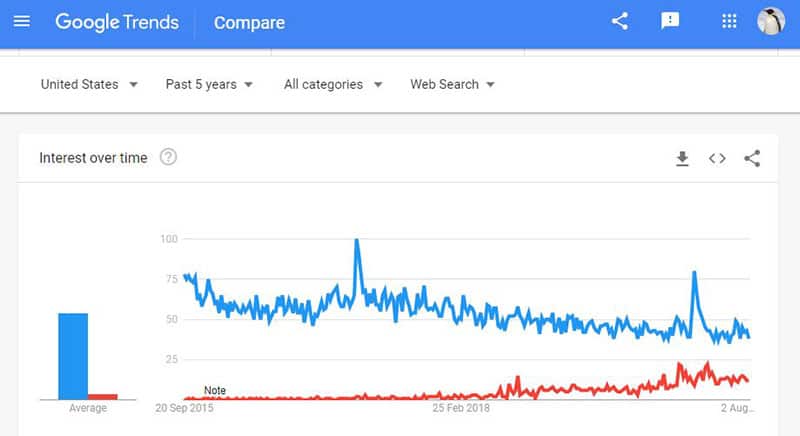
This suggests to me that in 5 years WireGuard could be the leader on this market, so it’s probably a good time to start learning more about this solution.
It doesn’t mean it’s a better solution, but more and more people are looking at it.
Security
Ok good, WireGuard may be faster and trendy, but the main criteria for a choice is still the security of our network. Is there a difference between both solutions?
OpenVPN is based on old technologies. SSL is over 20 years old and it’s one of the most popular solutions, that we still implement on almost any website for HTTPS.
WireGuard prefers new technologies, with ChaCha20-Poly1305, we don’t have so much experience, but in theory it’s faster and safer. Also, the low number of lines in its source code works in its favor to assume that everything is up-to-date and secure.
It’s really hard to choose a winner, or at least I don’t have enough knowledge in cryptography to choose.
For me, both are interesting, but your choice might still depend on your needs.
On a bigger company network, maybe the experience and popularity are more important that innovation and eventual instability.
At home with a Raspberry Pi server, WireGuard is probably an excellent solution.
It's a free PDF guide containing every Raspberry Pi Linux command you should know!
Download now
Reminder: Remember that all the members of my community get access to this website without ads, exclusive courses and much more. You can become part of this community for as little as $5 per month & get all the benefits immediately.
Conclusion
That’s it, you know the most important elements there is to know about OpenVPN and WireGuard. I tried to keep this post accessible for beginners, without going in too much technical details, so I hope it was enough for you and helped to give you a general idea on the topic.
If we focus again on the Raspberry Pi for the conclusion, I would say that WireGuard is probably the best solution to choose if you are installing a new VPN server today.
We don’t need manufacturers or other software developers to use it, so this limitation is not a problem. Also, stability is rarely the main criteria when we build something on Raspberry Pi, so even if there are some crashes sometimes, it’s ok (and I think it’s already stable enough to be used in production).
OpenVPN is still a good solution in some cases, but probably not with a Raspberry Pi server.
What do you think? Which one is your favorite? Why?
Are you interested in a step-by-step installation of WireGuard?
Whenever you’re ready, here are other ways I can help you:
The RaspberryTips Community: If you want to hang out with me and other Raspberry Pi fans, you can join the community. I share exclusive tutorials and behind-the-scenes content there. Premium members can also visit the website without ads.
Master your Raspberry Pi in 30 days: If you are looking for the best tips to become an expert on Raspberry Pi, this book is for you. Learn useful Linux skills and practice multiple projects with step-by-step guides.
The Raspberry Pi Bootcamp: Understand everything about the Raspberry Pi, stop searching for help all the time, and finally enjoy completing your projects.
Master Python on Raspberry Pi: Create, understand, and improve any Python script for your Raspberry Pi. Learn the essentials step-by-step without losing time understanding useless concepts.
You can also find all my recommendations for tools and hardware on this page.








