How to Install Kali Linux on Raspberry Pi? (Complete Guide)
Kali Linux is an open-source Linux distribution, based on Debian, that includes all apps for security experts and penetration testing. I tested it on my Raspberry Pi, and will share what I learned in this article.
Kali Linux is available directly in Raspberry Pi Imager, under “Other specific-purpose OS” in the “Choose OS” list. It can then be flashed on any SD card to start directly on any Raspberry Pi model (all versions are supported).
In this article, I will show you the two ways to install Kali Linux on your Raspberry Pi, and more important, how to get started with it once installed (including an introduction to some of the default apps).
If you’re looking to quickly progress on Raspberry Pi, you can check out my e-book here. It’s a 30-day challenge where you learn one new thing every day until you become a Raspberry Pi expert. The first third of the book teaches you the basics, but the following chapters include projects you can try on your own.
What is Kali Linux?

Kali Linux is a Debian-based Linux distribution that includes security and penetration testing tools.
Formerly known as Backtrack, many security companies (and also hackers) use it.
Associated with Raspberry Pi, it turns it into a perfect hacking kit. You may have seen it in the “Mr. Robot” TV series:
Kali Linux is available for the ARM architecture, so the installation is relatively simple. We will now discuss how to install it on your Raspberry Pi.
How to Install Kali Linux
Kali Linux has been recently added to Raspberry Pi Imager, so it’s the easiest way to install it on a Raspberry Pi. You can use this tool the same way as when installing Raspberry Pi OS, or download the image manually from the official website if you prefer.
I’ll show you both options in this tutorial. Sometimes, the manual download is better to get the latest image available.
Option 1: Use Raspberry Pi Imager
If you don’t already have Raspberry Pi Imager on your computer, you can download it from there on the official website.
I generally have it on my computer, and flash all my systems from it, but it’s also possible to use Raspberry Pi Imager on a Raspberry Pi if you don’t have a computer.
Once Raspberry Pi Imager ready, here are the steps to install Kali Linux on the SD card:
- Start Raspberry Pi Imager.
- Click on “Choose OS” to open the OS list.
- Go to “Other specific-purpose OS” and click on “Kali Linux”.
- You’ll get a list of all versions available, with the corresponding Raspberry Pi models:
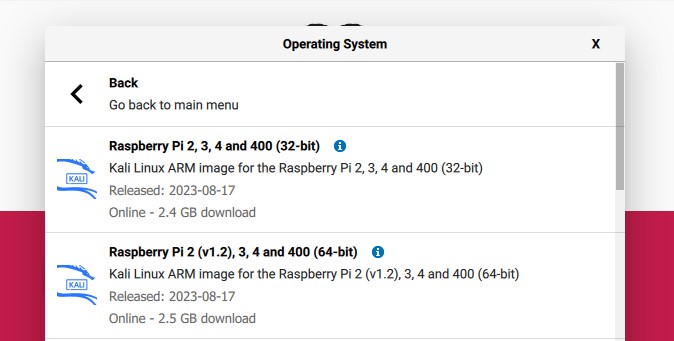
- Click on the version you want to install (64-bit is recommended if supported).
- Then click on the second button to pick your SD card (you can also use a USB drive if you prefer).
- And finally, click on “Write” to start the installation.
After a few minutes, Kali Linux should be ready to use, you can eject the storage device and plug it into the Raspberry Pi. Skip the option 2 below, and continue reading the tutorial with the first boot instructions.
Note: another option is to use the network boot feature if available, to flash directly Kali Linux from the Raspberry Pi, without the need of a previous operating system. Click on the previous link for more details about this.
Option 2: Download Kali Linux manually
Kali Linux images for the ARM architecture are available on this page of the official website.
Just make sure you’re on the list of ARM images (the Raspberry Pi’s architecture), and click on the image name or download icon to download it directly. You can also click on “Torrent” to download the torrent file.
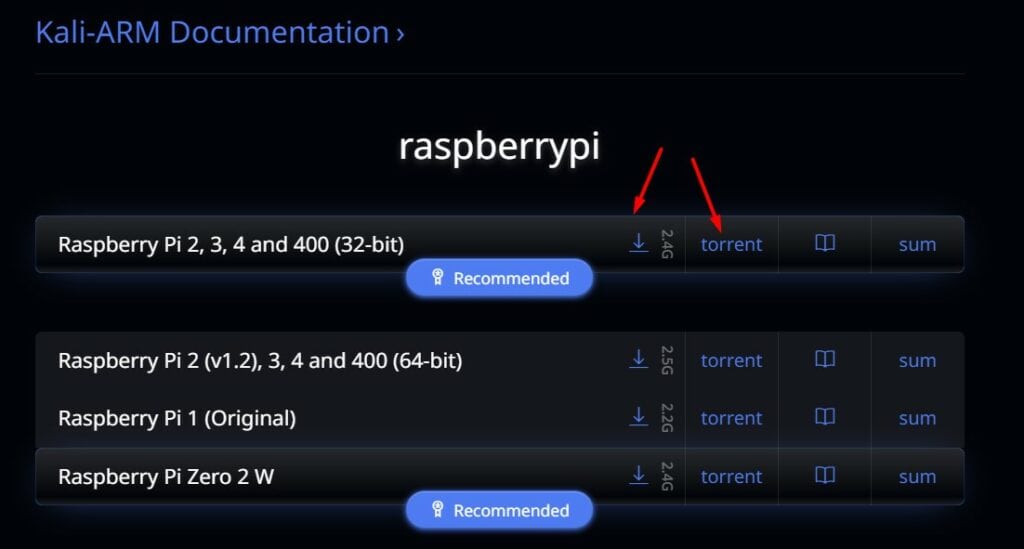
Torrent is a peer-to-peer download protocol (you can have even host a Torrent server on your Pi), sometimes it’s faster to download an image with it instead of the usual HTTP download, but it’s not mandatory.
As you can see, all Raspberry Pi models are now supported, from the original Raspberry Pi 1 to the latest models. So, you don’t have to worry, Kali Linux will run on your Raspberry Pi.
Once the image downloaded, you can either use Balena Etcher or Raspberry Pi Imager to flash it on a fresh SD card (or USB drive).
I won’t explain everything in details (check the previous links if you need more guidance), but basically, the main steps are:
- Get the Kali Linux image on your computer.
- Install and run Etcher or Raspberry Pi Imager.
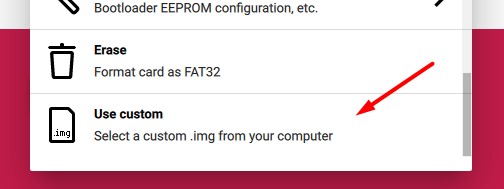
- Click on the first button to browse to the location of the Kali Linux image (on Imager, use “Use custom”).
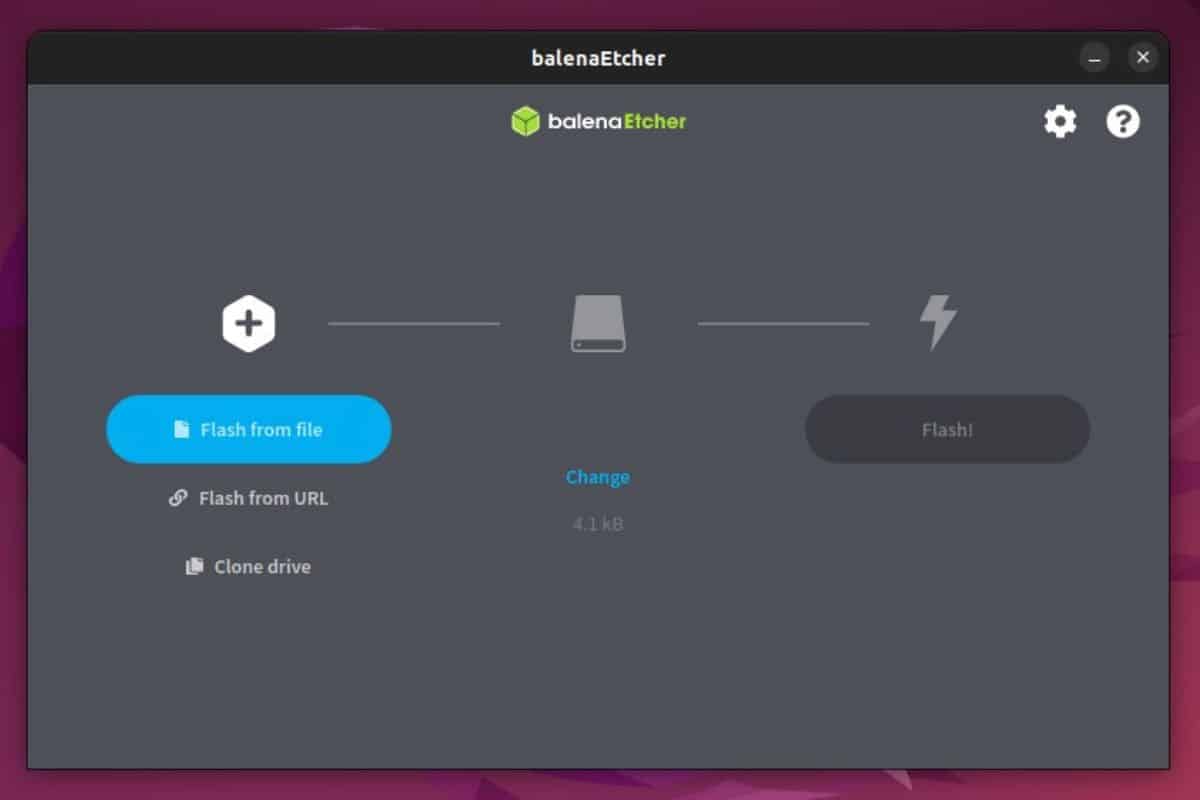
- Click on the second button to select the media (your SD card or USB drive).
- Click on the third button to start the process. It should take a few minutes to get done.
Getting started with Kali Linux on Raspberry Pi
No matter how you did the installation on the SD card, you are now ready to start Kali Linux for the first time on your Raspberry Pi.
It's a free PDF guide containing every Raspberry Pi Linux command you should know!
Download now
First boot on Kali Linux
Just insert the SD card into your Raspberry Pi and power it on.
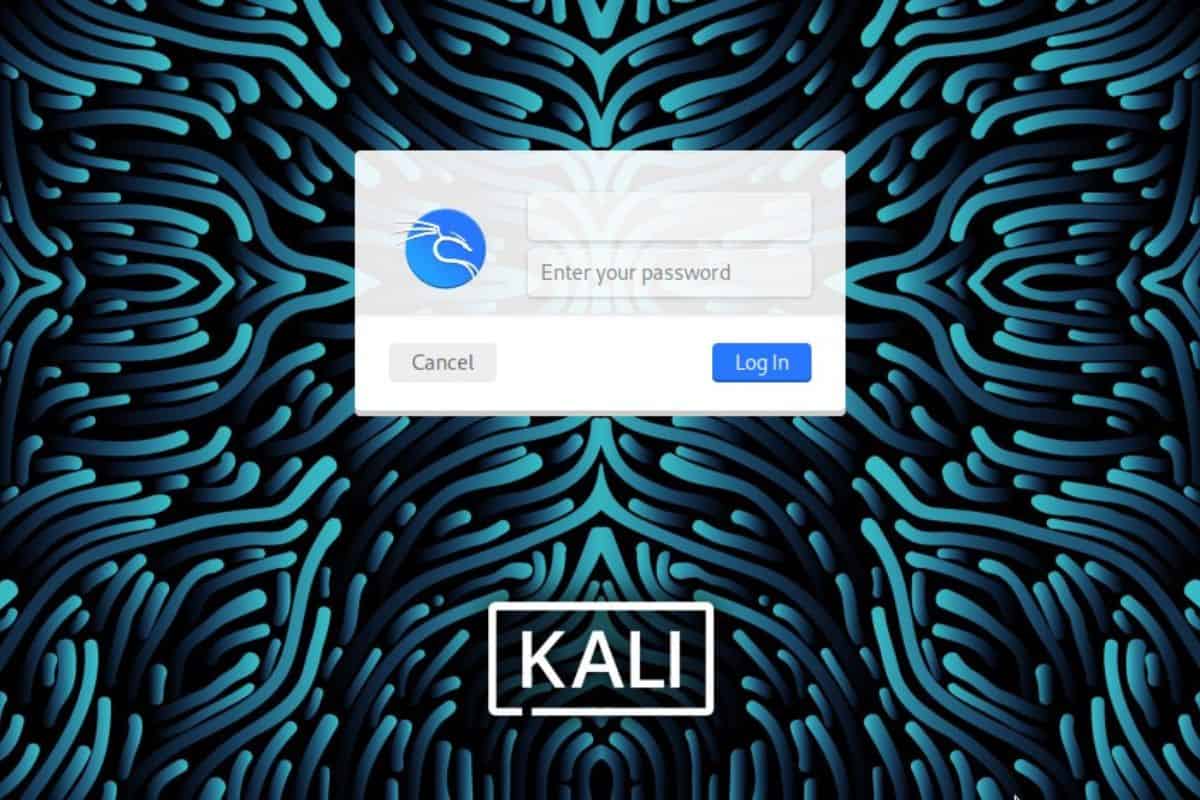
Kali Linux will start directly with the login screen.
No questions or anything, insert, start, and wait (the first boot might be longer, but it’s all running in the background).
There is nothing else to do.
Open a session on Kali Linux
Once Kali started, you need to log in:
On Raspberry Pi, the default Kali Linux username is “kali” with the same password “kali”.
Warning: the default keyboard layout is set to en-US, which mean you may need to type something like “kqli” if (like me) you use another layout.
You are now on the Kali Linux Desktop, and we can move to the configuration.

It is strongly recommended that you change these credentials quickly.
You can change it by opening a terminal and typing the command:passwd
Keyboard layout
If you don’t use a US keyboard, you can change it in the main menu > Settings > Keyboard.
Join Our Community!
Connect, learn, and grow with other Raspberry Pi enthusiasts. Support RaspberryTips and enjoy an ad-free reading experience. Get exclusive monthly video tutorials and many other benefits.
Learn more- Go to the “Layout” tab and disable the system defaults.
- Add your custom layout.
- Set it by default (or remove the US layout).
But be careful, on the login screen you will keep the US layout for the moment, so choose your password knowing this.
Connect to your Network (DHCP)
Follow this part only if there is a DHCP server on your network.
If not, or if you need to set a static IP address, look at the next section.
Ethernet:
If you can connect to an Ethernet network, it’s the easiest solution: simply connect the RJ45 cable to your Raspberry Pi and wait a few seconds for an IP address to be assigned to it, there is nothing else to do.
Wi-Fi:
The Raspberry Pi Wi-Fi card is supported natively, so connection to a wireless network shouldn’t be complicated either.
On the Kali desktop, click on the network icon at the top right, and choose the SSID of your Wi-Fi network.
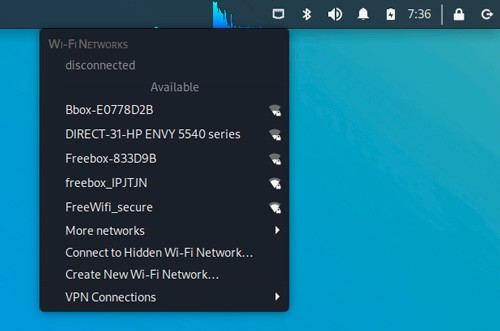
Type the password of your access point, and wait a few moments to be connected.
Get your current IP address:
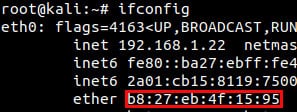
Whatever your connection mode, you can check the IP address obtained with the ifconfig command:ifconfig
The IP addresses are indicated on the second line of each interface, after the keyword “inet”.
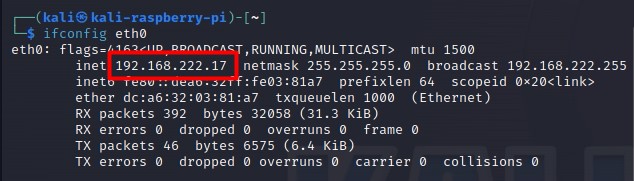
eth0 = Ethernet, wlan0 = Wi-Fi
I recommend not activating both interfaces simultaneously, even if it seems to work.
I had problems with response time by moments. Probably a problem with routing (I didn’t take any longer to look at this, but disabling the Wi-Fi fixed the problem).
Are you a bit lost in the Linux command line? Check this article first for the most important commands to remember and a free downloadable cheat sheet so you can have the commands at your fingertips.
Set a static IP address
A static IP address will allow you to choose the IP address associated with your Raspberry Pi, and therefore find it more easily later.
The easiest way is to use the GUI (find “Advanced network configuration” in the main menu), or via this tool in a terminal:sudo nmtui
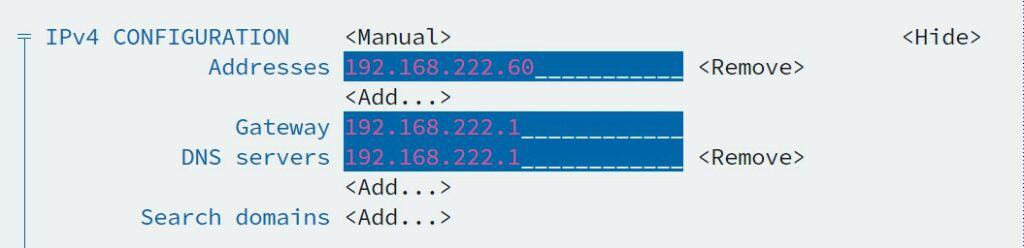
In it, you can configure your wireless network, but also set a static IP if needed.
But you also do the same thing manually, by directly editing the configuration file:
- Open a terminal or connect with SSH.
- To set a static IP, open the /etc/network/interfaces file:
sudo nano /etc/network/interfaces - You will see something like this:
auto eth0
iface eth0 inet dhcp - Replace it with something like this:
auto eth0
iface eth0 inet static
address 192.168.1.200
netmask 255.255.255.0
gateway 192.168.1.1
nameserver 8.8.8.8
Replace the IPs indicated by what fits your network. - Reboot your Raspberry Pi or unplug/plug the network cable to update your IP.
Update Kali
As for any fresh new installation, a good practice is to update your system.
Kali is based on Debian, so you can use the same commands as on Raspberry Pi OS:sudo apt update
sudo apt upgrade
Note: In my tests, I got this error when trying to upgrade: The following packages have unmet dependencies:
libwacom9 : Depends: libwacom-common (= 2.1.0-2) but 1.12-1 is to be installed
E: Broken packages
I fixed it with:sudo apt reinstall libwacom-common && sudo apt reinstall libwacom-bin
Then apt upgrade should work.
It's a free PDF guide containing every Raspberry Pi Linux command you should know!
Download now
By the way, I had approximately 800 packages to upgrade, so I think this is pretty important to do it right away.
Enable SSH and VNC
Now that we have a fixed IP address, it’s time to make our Raspberry Pi accessible from another network computer.
Enable SSH
In theory, SSH is installed and enabled by default.
If you don’t have access, it’s probably because you need to start the service:service ssh start
If you need help with SSH, look at this tutorial here.
Enable VNC
VNC will allow you to have access to a remote desktop on your Raspberry Pi.
On the latest Kali Linux versions, TightVNC is already installed.
You just need to set a password:
- Open a terminal or connect via SSH.
- Use this command to define your password:
vncserver - Once done, this will also start the service.
You can now connect to your Raspberry Pi on Kali Linux with any VNC Viewer.
For example, on Ubuntu:sudo apt install xtightvncviewer
xtightvncviewer 192.168.1.200:1
On Windows, you can download TightVNC here. Don’t forget to add “:1” after the IP address.
Remember that VNC is not a secure protocol, and if you use it at home it’s ok, but in a more extensive network, it is better to use it through an SSH tunnel for example.
You can find more details about the remote desktop on Raspberry Pi in my tutorial linked here. It’s for Raspberry Pi OS, but it’s very similar.
Note: If you get a gray screen when connecting to Kali Linux with VNC Viewer, you may need to edit the startup file for VNC:sudo nano ~/.vnc/xstartupPaste these lines (backup the old content if needed): !/bin/sh
unset SESSION_MANAGER
unset DBUS_SESSION_BUS_ADDRESS
startxfce4 &
[ -x /etc/vnc/xstartup ] && exec /etc/vnc/xstartup
[ -r $HOME/.Xresources ] && xrdb $HOME/.Xresources
xsetroot -solid grey
vncconfig -iconic &
Kali Linux tools
Ok, your basic configuration of Kali Linux is now ready. You could obviously use it as a standard desktop operating system, but I guess if you installed Kali, it’s probably that you’re interested in some of the default apps that come with it.
Let’s list a few of them with a short demonstration of how they work. This isn’t an exhaustive list of complete tutorials for each one, but it will give you a better idea of the possibilities.
Change your MAC Address
Overview
A MAC address is a unique identifier for each network adapter. It depends on each manufacturer, and it’s often used to give access to a specific part of the network to restricted computers. A DHCP server can also assign always the same IP to a MAC Address.
For example, you can configure your Wi-Fi network to whitelist your MAC address, and prevent anyone else from connecting to it. I have a detailed article here on how to find the MAC address of your Raspberry Pi.
MacChanger is a tool that allows you to do MAC address spoofing, i.e. to pretend to be someone else.
Usage
Install it if needed (in my tests it was already installed):sudo apt install macchanger
See your current MAC Address:ifconfig eth0
- Disable your network card:
ifdown eth0 - Get a random MAC address:
macchanger -r eth0 - Set a specific MAC address:
macchanger -m XX:XX:XX:XX:XX:XX eth0 - Reboot to reset and get the standard MAC Address.
Hack Wi-Fi password
Overview
AirCrack-NG is one of the most popular tools on Kali Linux.
It’s a complete suite of tools to test the wireless security of a network.
It provides tools for monitoring, attacking, testing, and cracking Wi-Fi networks.
Usage
You need to disconnect the Wi-Fi on your Raspberry Pi before starting:
- Then check that your network card is compatible (it is):
sudo airmon-ng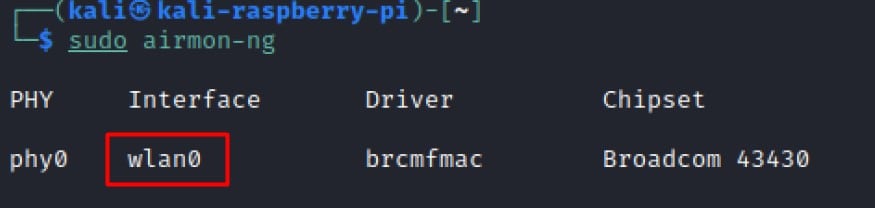
- Start monitoring:
sudo airmon-ng start wlan0 - Show wireless network available:
sudo airodump-ng wlan0mon
And you are ready to go!
You can read this post to get more details on how to do this.
Brute force with Hydra
Overview
Brute force is a password cracking method, that tries passwords from a dictionary or other sources, and tries all the possibilities until it works.
Hydra is a tool to make very fast brute force from Kali Linux software and that supports many protocols.
Usage
First, you will need a list of passwords and put it in a file, like /root/passwords.txt (one per line).
You can find the most common passwords on the Internet, or generate your own.
For the test, just put a few random passwords manually in the file.
Then you can try it, for example, I have decided to brute force SSH on my computer from the Raspberry Pi:hydra -l root -P /root/passwords.txt -t 6 ssh://192.168.222.51
If I check in my /var/log/auth.log, I can see tries from the Raspberry:
May 22 15:55:37 ubuntu sshd[2481]: Failed password for root from 192.168.222.31 port 37226 ssh2 May 22 15:55:37 ubuntu sshd[2487]: Failed password for root from 192.168.222.31 port 37234 ssh2 May 22 15:55:39 ubuntu sshd[2482]: Failed password for root from 192.168.222.31 port 37228 ssh2 May 22 15:55:39 ubuntu sshd[2484]: Failed password for root from 192.168.222.31 port 37232 ssh2
Packet Analyzer
Overview
A packet analyzer (or sniffer) is a tool that can intercept traffic from the network and capture it to analyze it.
On Kali Linux, you can use Wireshark, which is the most used tool to analyze network traffic.
It’s a graphical tool, but you can capture packets with tcpdump or something else, and then open it with Wireshark.
Usage
You can find the app in the Applications menu, under Sniffing and spoofing:
- Start it and then go to Capture > Start.
- You will now see all packets from the network.
- Click Stop when you want.
Then there are many features that you can use to filter or analyze what you have captured:
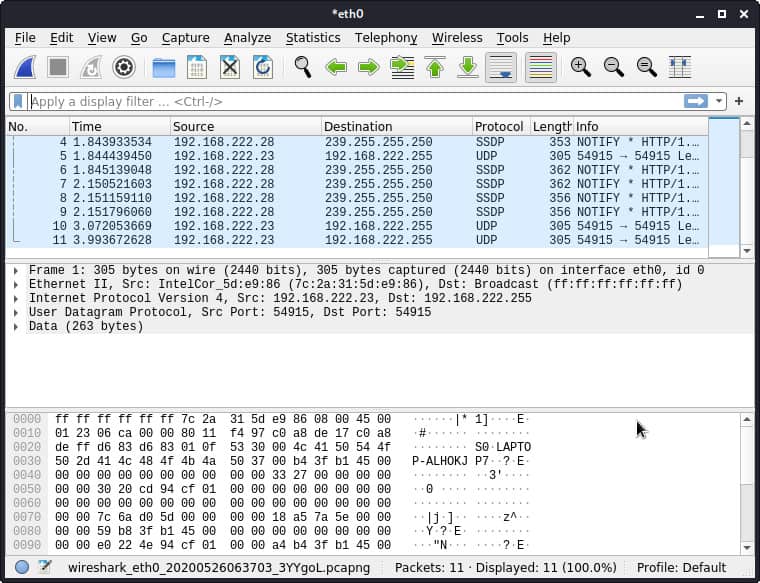
Related: Getting Started With Wireshark On Ubuntu
SQL Injection
Overview
SQL injection is a technique to attack insecure applications, including injecting code into user fields that are not protected.
This technique is mainly used to attack websites.
For example, if you replace a parameter of the URL, say ?user=yourname with something like ?user=yourname ‘ OR 1.
If the field is poorly protected, the SQL query will be modified and will return all the data, not just those of your user.
On Kali Linux, the sqlmap tool allows testing SQL injection vulnerabilities.
Usage
Sqlmap is a straightforward tool to use.
You only need to put the URL of the page to test, something like this:sqlmap -u https://www.domain.com/?p=123
Once you have found a security hole, it is possible to dig deeper with this tool to see what you can get. But the best thing to do is to fix it.
Vulnerabilities exploit
Overview
Metasploit is a tool that will allow you to validate vulnerabilities and use them.
Metasploit allows you to automate the process of discovery and exploitation and provides you with the tools required to perform the manual testing phase of a penetration test.
Usage
You can start it in Applications > Exploitation Tools > Metasploit framework.
This tool will initialize and start a terminal that will allow you to use it.
For example, you can use nmap in the framework:db_nmap -v -sV 192.168.222.1
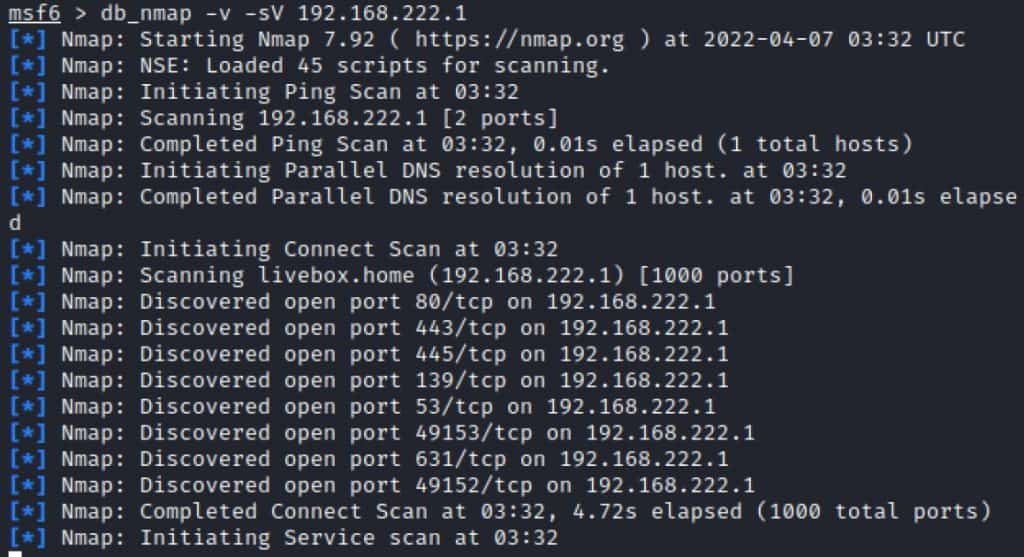
You can also retrieve information about a known vulnerability, and try to use it:db_rebuild_cache
search CVE-2018-9864
use exploit/folder/folder/name
Replace the search parameter with your vulnerability ID and use the exploit path displayed in the search results.
If you are interested, find a good tutorial on the topic (or read the documentation), it’s not possible to explain everything in a few short lines.
It's a free PDF guide containing every Raspberry Pi Linux command you should know!
Download now
Video
If you want a visual explanation, you can watch this video on how to install Kali Linux on your Raspberry Pi:
Subscribe to get all the other videos about Raspberry Pi:
It's a free PDF guide containing every Raspberry Pi Linux command you should know!
Download now
If you are looking for exclusive tutorials, I post a new course each month, available for premium members only. Join the community to get access to all of them right now!
Conclusion
We have seen how to install Kali Linux on Raspberry Pi, including the first steps of the system configuration, and some exciting tools to use on this distribution.
As I said at the beginning, this article is not exhaustive. There are hundreds of apps and most are quite complicated to take in hand, which would require an article each, but that was not the goal here (in fact, I have another website about Kali Linux that you can check if you’re interested in this topic).
I hope this article was helpful anyway. Check the links below for more interesting resources about the Raspberry Pi world.
Whenever you’re ready, here are other ways I can help you:
The RaspberryTips Community: If you want to hang out with me and other Raspberry Pi fans, you can join the community. I share exclusive tutorials and behind-the-scenes content there. Premium members can also visit the website without ads.
Master your Raspberry Pi in 30 days: If you are looking for the best tips to become an expert on Raspberry Pi, this book is for you. Learn useful Linux skills and practice multiple projects with step-by-step guides.
The Raspberry Pi Bootcamp: Understand everything about the Raspberry Pi, stop searching for help all the time, and finally enjoy completing your projects.
Master Python on Raspberry Pi: Create, understand, and improve any Python script for your Raspberry Pi. Learn the essentials step-by-step without losing time understanding useless concepts.
You can also find all my recommendations for tools and hardware on this page.





perhaps you can help me with something.i’m trying to remote to a raspberry pi from a phone then start a pentest.but the catch is i have the pi in a coat pocket.giving the appearance i’m just playing on my phone.all the while using my tools on kali while walking through a site i’ve been tasked with.basicly (phone-raspberry pi(in pocket)-wireless router-loot)ideas?
This article was extremely helpful. It explained important things that YouTube tutorials did not.
Thanks Maya 🙂
Thanks for the very explained tutorial, it teaches much more than just intallation!
I’m having an issue with the network devices. I’m not sure, but after the update and upgrade or after I changed the interfaces file as you suggested and rebooted the Pi there is the message “device not managed” under the “Ethernet Networks” and Wo-Fi Networks”.
Could help me?
Thanks
Hi Eduardo,
I have no idea, I didn’t get this error in my test
But you can probably check this link: https://www.blackmoreops.com/2013/11/25/how-to-fix-wired-network-interface-device-not-managed-error/
Let us know if it’s ok after that, I can edit this post to add the solution if everyone get this error now
Hello,
I just updated this post today
Mainly for the installation part as there are a few changes in the last updates
The Raspberry Pi 4 is now supported (if you download the good image version…)
i dont have another computer,is there a way to flash image using rasbian on raspberry pi.plzzzz reply caus i need help and does 64 bit kali version works on raspberry pi 4?
Hi,
I think you can install Etcher on your Raspberry Pi and a USB/SD Card reader like this one:
https://amzn.to/2YAef2V
I never tried, but it should work
Patrick
This guide is very complete. But i have a problem. When I do the command: sudo apt upgrade, at the moment that the percentage is 15% the screen goes black and rebooting doesn’t solve it. If you got an idea of what I’m not doing or anything, tell me please. I keep reinstalling kali and try different things.
Raspberry 4b 4gb
Kingston 32gb 10
Also I used the Raspberry Pi Imager
Maybe you can try this via SSH, so that even if the display driver is updated you can still see the upgrade progress.
i just found this site. Not just a basic knowledge, but very interesting. Thanks so much.
Good article, it’s awesome . But how can I use Rpi GPIO with Kali Linux
When I try it on raspberry pi 400 by my self i just get stuck on the code from the boot yea thar no moving code or code with bracets where inside have a green V as usual. When i use the card on my rpi 4 it works completly normal. What is going on I cant even see the login session and bringing my big razer keyboard on trips for the rpi4 it is not the best idea. Please help
Hi,
Make sure you use the image version made for the RPI 400.
There is a specific image on the download page.
It’s the same as Pi 4, but if you have an old image it may not be compatible.
Patrick